Permit MCP Gateway
Drop-inTrust Layerfor MCP
Authentication, fine-grained authorization, consent, and audit—so your agents can move fast without turning your SaaS and data into open desert.

The Agentic
Spice Must
Flow.
Deploy AI agents with confidence.
Real-time visibility, intelligent detection,
and enterprise-grade security.

Platform Overview
Secure your agents with zero code changes
- Real-time visibility into every agent action
- Intelligent detection of risky behavior
- Enterprise-grade security and compliance
See It In Action
From Sign-In to Audit Trail
01/04
Works With Every MCP Server You Already Use
Drop-in proxy for any MCP server. No changes to your existing setup.
https://your-gateway.agent.security/mcp?upstream_mcp=https://api.salesforce.com/platform/mcp/v1-beta.2/sobject-all
https://your-gateway.agent.security/mcp?upstream_mcp=https://api.githubcopilot.com/mcp/
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.slack.com/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://gdrive.googleapis.com/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.atlassian.com/v1/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.atlassian.com/v1/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.hubspot.com
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.notion.com/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.linear.app/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.neon.tech/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.stripe.com
https://your-gateway.agent.security/mcp?upstream_mcp=https://<account>.snowflakecomputing.com/api/v2/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.mongodb.com
https://your-gateway.agent.security/mcp?upstream_mcp=https://knowledge-mcp.global.api.aws
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.figma.com/mcp
https://your-gateway.agent.security/mcp?upstream_mcp=https://mcp.zendesk.com/mcp
Built for Developers. Trusted by Security.
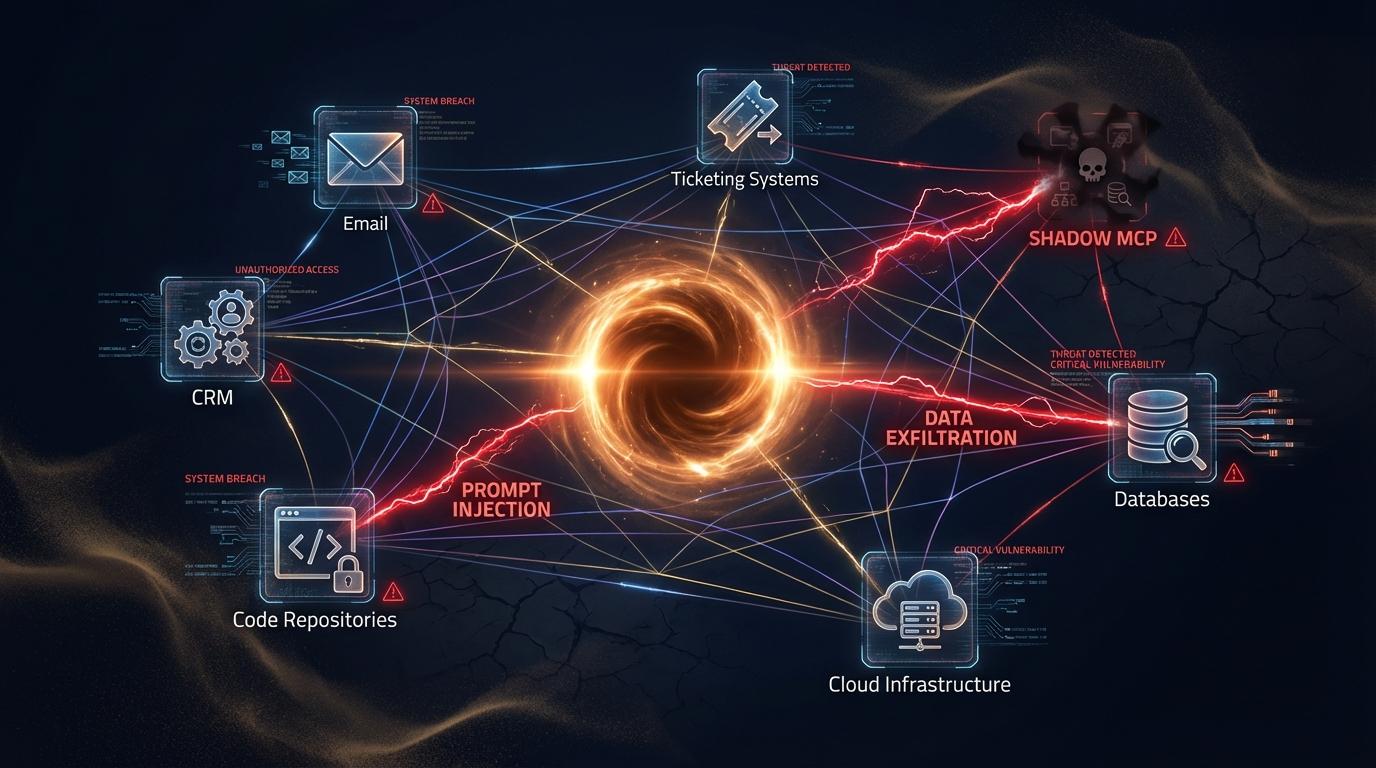
MCP Makes Every Tool
a Wormhole.
Your agents can reach Notion, Google, Salesforce, ticketing, code, infra—in milliseconds. That's powerful. It's also a new blast radius.
- Prompt injection & unintended actions
- Data exfiltration across boundaries
- “Shadow MCP” connections you don't see
Gartner's take: As agentic AI expands, organizations will need “guardian agents” that observe and enforce policy at runtime to keep AI reliable and secure.
Permit MCP Gateway is the runtime enforcement layer—
Purpose-built for Identity + Delegation + Least Privilege
What the Gateway Actually Does
Six layers of security that sit between your agents and your MCP servers. You configure once; the gateway enforces on every call.
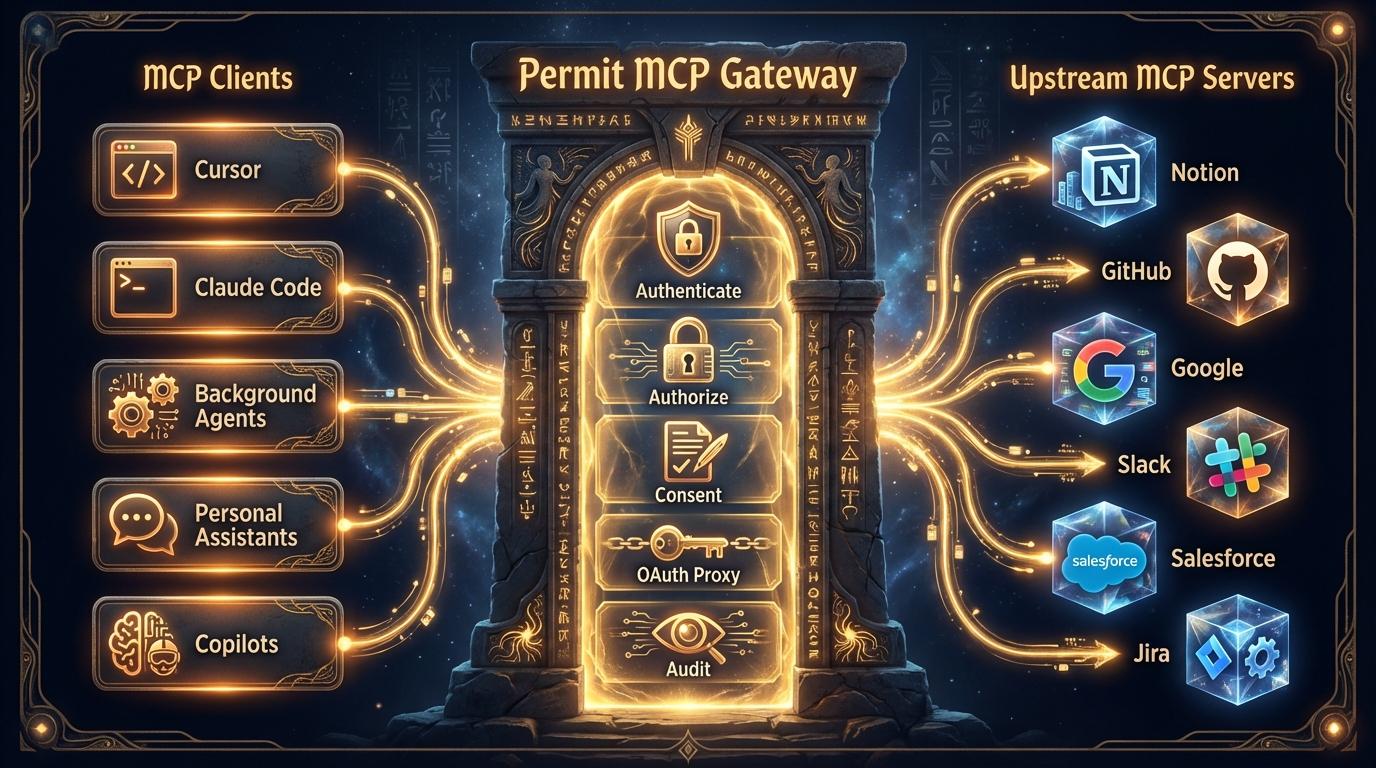
OAuth 2.1 Authentication
Connect your existing IdP—the gateway handles OAuth 2.1 flows, token exchange, sessions, and refresh automatically. No custom auth code required.
Fine-Grained Authorization
Every tool call checked against OPA policies that are auto-generated for your stack. Supports RBAC, ABAC, and ReBAC—pick your model, we enforce it.
Consent Editor
Build white-labeled consent screens with the visual editor. Your branding, your rules, IAM-governed. No frontend work needed.
Identity & Agent Provisioning
Auto-provision agent identities from your IdP. Policy-based relationships between humans and agents. Plugs into IGA, PAM, IAM.
Centralized Governance
One control plane for every MCP decision. Real-time monitoring, anomaly detection, compliance reporting—across all servers.
Decision Logs & Auditing
Full decision chain: user, agent, tool, policy, outcome. Searchable, exportable, SIEM-ready.
It's As Easy As 1-2-3
No SDK to install. No agents to rewrite. No MCP servers to modify.
Just configure, consent, connect.
Add Your MCP Servers
Auto-Generated Policies
Point the gateway at your MCP servers. It inspects available tools and generates a contextual authorization policy for each one. You pick the trust level; the gateway writes the OPA policy.
Set Up Consent Screens
Visual Editor, Your Brand
Build white-labeled consent flows with the visual editor. Decide which tool calls need user approval, what gets shown on the consent screen, and who governs the rules. No frontend work needed.
Hand Over the URL
Same Protocol, New Powers
Give developers and users the proxied MCP endpoint. Auth, authorization, consent, and logging all happen at the gateway. The MCP protocol stays the same, so nothing breaks downstream.
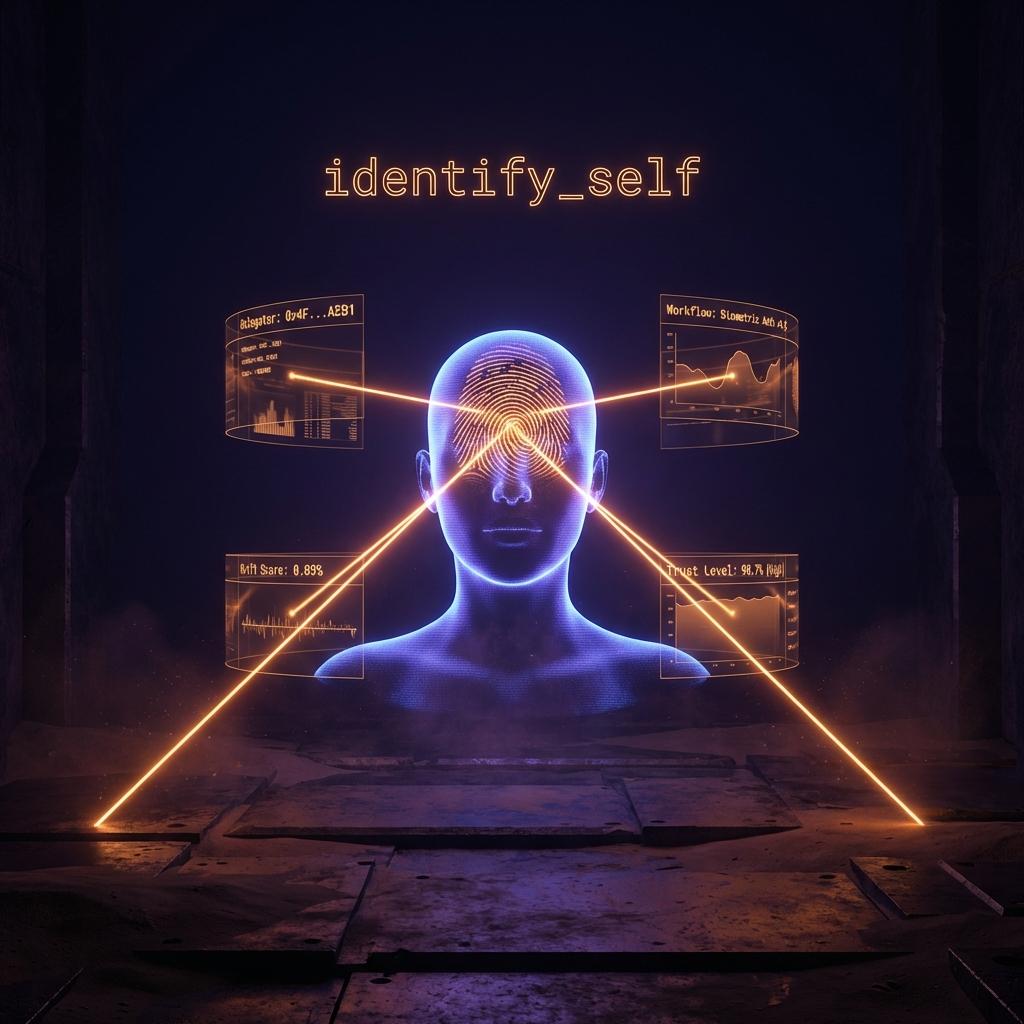
Agent Identity
That Doesn't Lie.
Before any tool is exposed, the gateway requires a single handshake: identify_self. It fingerprints the agent and continuously monitors for drift—so you always know exactly what's connecting.
- Human delegation — who authorized this agent and what they consented to
- Context — relationship graph to tools, data, and workflows
- Agent intent — behavioral fingerprint from interrogation, with drift detection
Prevents: Shared client sessions, reused permissions, and invisible privilege escalation.
Features Built for the Storm
Every capability designed to survive the chaos of agentic AI at scale—no gaps, no workarounds.
Humans
Drop-in Authentication
Bring your IdP. Authenticate delegators via SSO/OIDC and attribute every action to a verified human.
Agents
Fine-Grained Authorization
Get auto-generated policies you can edit in OPA/Rego, plus a Google Zanzibar-inspired relationship graph that powers ReBAC for real-world delegation and multi-hop access chains.
Your Security Team Won't Hate
Consent UX
Trust slider for tiered trust. Tool picker for explicit allowed tools. Auto-trust heuristics to reduce friction.
Zero Credential Exposure
OAuth Proxy + Vault
Gateway handles OAuth flows, stores tokens in a vault, and issues the agent a stand-in token. Zero standing permissions.
By Default
Observability & Audit
Every decision becomes an audit trail: what happened, when it happened, and why it was allowed or denied.
Drift Detection
Agent Fingerprinting
Detect prompt drift before it becomes an incident. Interrogate. Fingerprint. Enforce.
AI watchers that monitor, adjust, and enforce.
Gartner calls them “guardian agents”—AI-native watchers that observe every action and adjust policies on the fly. Permit provides the dynamic, fine-grained control plane and enforcement point they need to act in real time.

Monitor
Observe every agent action, tool call, and data access in real time
Adjust
Dynamically update policies on the fly based on risk signals and drift
Enforce
Fine-grained enforcement using agentic identity: human delegation, context, and intent
Consume or Provide.
Secured Either Way.
Securely Consume
MCP Servers
For Internal Agents
Allow Cursor, Claude, and internal agents to use MCP safely. Stop incidents on sensitive surfaces—email, CRM, files, ticketing.
- →Roll out agentic AI for everyone—with control
- →Prevent AI incidents on sensitive surfaces
- →Control who can use what
Provide Secure
MCP Servers
For Your Customers
If you expose MCP as a product surface, get multi-tenant, policy-driven authorization with customer-specific consent and trust tiers.
- →Multi-tenant authorization out of the box
- →Customer-specific consent + trust tiers
- →Audit trails and delegated access that scale

Why Permit
Others secure a layer. Permit secures the chain.
Most “MCP security” products stop at the gateway. Permit's advantage is years building the authorization control plane underneath.
- High-performance PDP with sub-10ms decisions
- Policy-as-code + relationship graph
- Real-time updates via OPAL
As agentic AI collapses boundaries, the identity stack converges: IGA + PAM + Zero Trust + IAM acting as one system—real-time, dynamic, and fine-grained.
Your Infrastructure. Your Rules.
Permit's hybrid architecture decouples control plane from data plane—keep enforcement close to workloads and push policy updates in real time via OPAL.

Hosted (Self-Serve)
Start in minutes. No infrastructure to manage. Permit handles the control plane so you can focus on building.
On-Prem / In Your VPC
Keep enforcement and sensitive flows in your environment. Full control over your data plane with Permit's PDP deployed alongside your workloads.
Enterprise Security. Battle-Tested.
- ✓SOC 2 Type II — Security, Availability, Confidentiality (Dec 2023 – Nov 2024)
- ✓Cloud-first posture — Infrastructure via AWS, no physical servers
- ✓Secure SDLC — Code review, vulnerability scanning, audited controls
- ✓HIPAA / GDPR / CCPA — Compliant. ISO 27001 compatible, certification in progress.

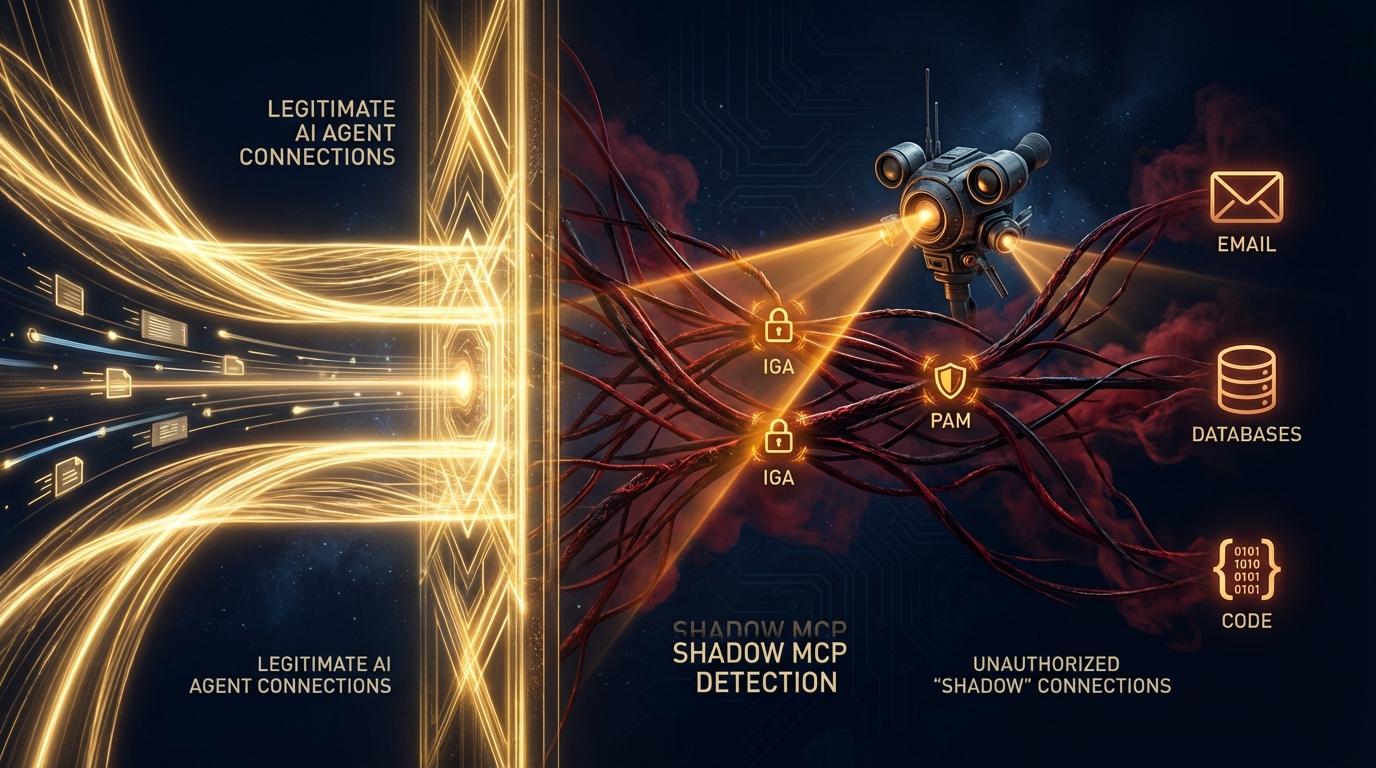
IGA / PAM Connectors
for Shadow MCP
Agents won't always go through the gateway. So we're adding connectors that detect, alert, and block when agents touch sensitive surfaces outside.
- Detect agents on sensitive surfaces outside the gateway
- Alert and block via the IAM of each surface
- Drive the org toward a single “Agentic Zero Trust” path
“For the first time, we see what’s really happening inside our agentic stack. When something deviates, we know it’s real.”
Enterprise Security Leader
Let Your Agents
Ride the Storm.
We'll make sure they only go where they're allowed.
Or schedule a call with the Permit team →
